How much of your daily digital life actually stays confidential? From banking details to private messages, modern communication relies on invisible safeguards most users never see. We’ll show why understanding these digital locks matters for everyone – not just tech experts.
At its core, data protection transforms readable information into scrambled code using mathematical formulas and secret passwords called keys. Popular methods like AES and RSA act as virtual vaults for sensitive transactions and cloud storage. Without them, hackers could intercept credit card numbers or medical records with shocking ease.
Businesses face growing pressure to shield customer details while maintaining operational speed. Individuals risk identity theft when personal data travels unprotected across networks. By learning how these security layers work, you gain control over what stays hidden – and from whom.
This guide breaks down essential concepts without technical overload. We’ll explore how different security types fit specific needs and why choosing the right software matters. Ready to stop leaving digital footprints in plain sight?
Understanding Encryption Fundamentals
Imagine your digital data as a locked diary – only those with the right key can read its contents. This simple analogy captures the essence of modern data protection. At its core, encryption acts like a mathematical translator, turning sensitive information into unreadable code during transmission or storage.

What Is Encryption?
We define this process as scrambling readable text (plaintext) into secret code (ciphertext). A key – either identical or paired – determines how the information gets transformed. As cybersecurity expert Bruce Schneier notes:
“Encryption is the most effective way to achieve data security.”
How Does Encryption Work?
Two primary methods dominate digital security:
- Symmetric systems use one key for locking and unlocking
- Asymmetric systems employ separate public/private keys
When you log into your bank account, algorithms like AES-256 create temporary codes that change with every session. This ensures even intercepted data remains useless to attackers. Modern protocols verify both message authenticity and sender identity – crucial for legal documents or financial transfers.
Businesses rely on these mechanisms to protect customer records, while individuals benefit from secured messaging apps. Choosing the right security approach depends on your specific needs – whether guarding personal photos or corporate trade secrets.
The Role of Encryption in Protecting Sensitive Information
Trust forms the backbone of every digital interaction. When sharing sensitive details online, you need assurance that prying eyes can’t access or alter your information. Modern security methods go beyond scrambling content—they verify its authenticity and origin.
Ensuring Confidentiality and Integrity
Confidentiality means only authorized parties view your data. Think of medical records sent between doctors—security protocols ensure they remain private during transit. Integrity guarantees information stays unchanged. Tools like SHA-256 hash functions create unique digital fingerprints for files. If even one character changes, the fingerprint becomes unrecognizable.
Financial institutions use these checks to spot tampered transactions. A single altered digit in a bank transfer would trigger immediate alerts. This dual protection builds trust in systems handling critical operations.
Authentication and Nonrepudiation Explained
Security methods also confirm who sent the data. Digital signatures act like virtual ID cards, linking messages to specific users. As cybersecurity analyst Lisa Mitchell explains:
“Authentication stops imposters, while nonrepudiation stops liars.”
Nonrepudiation provides legal proof of communication. Courts accept these digital trails as evidence because they’re nearly impossible to fake. This combination protects businesses from fraud and ensures accountability in sensitive exchanges.
Encryption: Essential Methods to Secure Your Data
What keeps sensitive files and financial records safe during digital transfers? The answer lies in standardized protocols that balance accessibility with ironclad security. Among these, one method stands as the backbone of modern information safety.
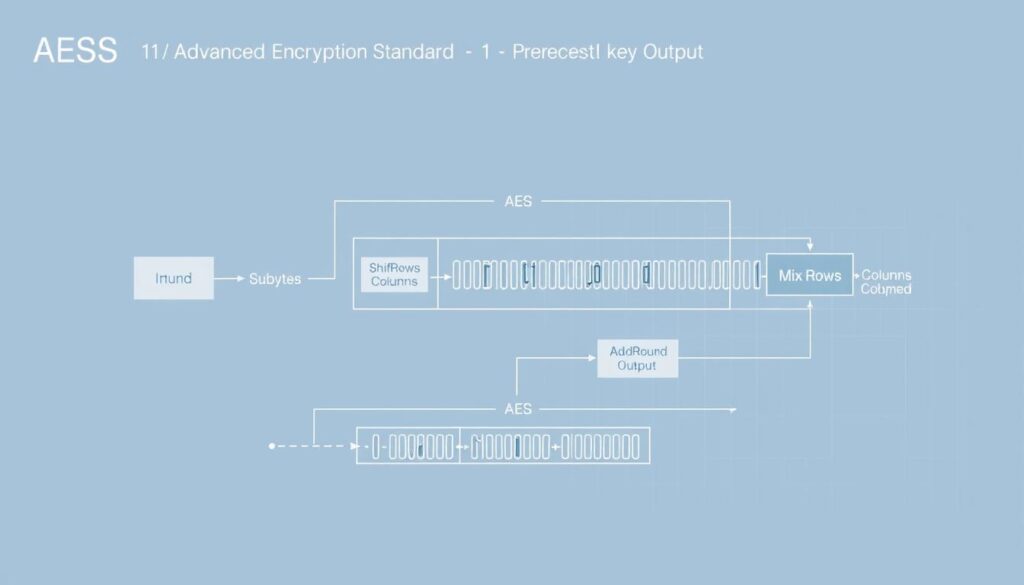
Breaking Down the Advanced Encryption Standard
Developed by the National Institute of Standards and Technology (NIST), AES revolutionized digital security through its symmetric block design. This approach processes data in fixed 128-bit chunks using three key strengths:
- 128-bit keys – Ideal for everyday security needs
- 192-bit keys – Enhanced protection for sensitive records
- 256-bit keys – Military-grade safeguarding for critical infrastructure
Financial institutions and government agencies worldwide rely on this standard. As cybersecurity researcher Dr. Alan Torres explains:
“AES transformed how we protect digital assets – its mathematical foundation resists even sophisticated attacks.”
The method’s efficiency allows rapid processing without compromising safety. Whether securing cloud storage or authenticating payment gateways, AES adapts to various scenarios through ten to fourteen transformation rounds per data block. This flexibility explains why it became the first publicly accessible standard approved for classified U.S. government information.
Upcoming sections will contrast this approach with alternative security strategies. Understanding AES’s role helps businesses and individuals choose appropriate safeguards for their specific needs.
Comparing Symmetric and Asymmetric Encryption
How do modern security systems balance speed with airtight protection? The answer lies in choosing between two foundational approaches – one built for efficiency, the other for secure collaboration. Let’s examine why organizations often mix both strategies to meet evolving threats.

Benefits and Drawbacks of Symmetric Methods
Symmetric encryption operates like a high-speed vault – it uses a single secret key to lock and unlock data. This method powers banking transactions and enterprise databases where speed matters. Popular algorithms like AES process terabytes of information faster than most alternatives, making them ideal for large-scale operations.
However, sharing the secret key securely poses challenges. As cybersecurity expert Mark Thompson warns:
“A symmetric system is only as strong as its key distribution protocol.”
If hackers intercept the key during exchange, entire communication channels become vulnerable. This limitation explains why many systems pair symmetric methods with other security layers.
Organizations favor this approach for internal data storage or closed networks where key management stays controlled. Its efficiency shines when handling massive datasets – think hospital records or financial ledgers. For scenarios requiring external collaboration, hybrid models often combine symmetric speed with asymmetric verification.
Data Encryption Applications and Cloud Security
Modern businesses increasingly rely on cloud platforms – but how do they keep sensitive files safe across shared servers? The answer lies in protecting data both at rest (stored) and in transit (moving). Without these dual safeguards, confidential records could leak during uploads or sit vulnerable in storage databases.

Guarding Data Wherever It Lives
Data at rest requires protection from physical theft or unauthorized access. Cloud providers often use encryption-as-a-service (EaaS) to scramble stored files automatically. For stricter control, some companies opt for BYOE (bring your own encryption) models, letting them manage security keys independently.
Network transfers demand equal vigilance. Financial analyst Sarah Nguyen notes:
“Unsecured data in motion is like shouting credit card numbers in a crowded room – everyone hears it.”
Secure protocols like TLS create temporary tunnels for information traveling between devices. This prevents interception even on public Wi-Fi. Multi-tenant cloud environments benefit most – strong encryption ensures your data stays isolated from other users.
Effective strategies combine both approaches. Regular key rotation and access audits add extra layers. By integrating these practices, organizations build trust while meeting compliance standards like HIPAA and GDPR.
Overcoming Challenges in Encryption Key Management
The weakest link in digital security often isn’t the algorithm – it’s the human handling of access codes. Proper key management determines whether sensitive information stays protected or becomes exposed. Organizations lose data permanently when keys get misplaced, while attackers exploit poorly stored credentials.

Best Practices for Protecting Your Keys
Centralized key management systems reduce risks by automating storage and access controls. We recommend:
- Storing keys separately from encrypted data
- Rotating credentials every 90 days
- Auditing access logs weekly
Cybersecurity architect Dr. Emily Carter notes:
“Treat keys like crown jewels – limit who touches them and track every movement.”
Multi-cloud environments demand extra care. Use hardware security modules (HSMs) for physical protection against unauthorized access.
Mitigating Brute-Force and Side-Channel Attacks
Brute-force attempts overwhelm systems with endless password guesses. Strong keys with 256-bit length increase cracking time to centuries. Side-channel attacks target indirect clues like power usage patterns.
Countermeasures include:
- Rate-limiting login attempts
- Masking cryptographic operations
- Using constant-time algorithms
Disaster recovery plans prevent data loss during crises. Test backup key retrieval quarterly – a single oversight could lock critical files forever.
Best Practices for Implementing Encryption Solutions
Businesses today juggle aging infrastructure and cutting-edge platforms – how do they secure both without breaking workflows? Effective data protection requires bridging technological generations while maintaining airtight safeguards.
Integration with Legacy and Modern Systems
Hybrid IT environments demand tailored approaches. Start by mapping where sensitive data flows – from on-premises servers to cloud APIs. Compatibility issues often arise when connecting older systems with modern security protocols.
We recommend these strategies for seamless integration:
- Phase upgrades using middleware that translates between old/new security standards
- Centralize key management across all platforms through unified dashboards
- Conduct quarterly audits to identify outdated protocols needing replacement
Cybersecurity architect Priya Kapoor emphasizes:
“Treat legacy systems like museum artifacts – handle with care but don’t let them dictate your security roadmap.”
Cloud-based solutions often simplify this process. Many providers offer API gateways that wrap older applications in modern security layers. This lets enterprises maintain critical operations while adopting advanced protection measures incrementally.
Prioritize solutions that meet compliance standards like PCI DSS and HIPAA. Automated monitoring tools help track data flows across mixed environments, flagging vulnerabilities in real time. Remember – consistent protection requires equal vigilance across every system touchpoint.
Future Trends in Encryption and Cybersecurity
Digital security stands at a crossroads as emerging technologies reshape protection paradigms. Organizations now face a dual challenge: defending against sophisticated threats while adapting to revolutionary tools that could redefine privacy standards.
Quantum Security and Machine Learning
Quantum computing threatens current security methods by potentially cracking traditional algorithms in minutes. Researchers counter this with quantum key distribution (QKD) – a method using light particles to create unhackable communication channels. Early adopters like financial institutions already test these systems for ultra-secure transactions.
Artificial intelligence transforms how we approach data safety. Machine learning models now:
- Generate dynamic keys that evolve during transmission
- Detect abnormal network patterns 83% faster than human teams
- Predict vulnerability hotspots using historical breach data
Cybersecurity futurist Dr. Rachel Kim observes:
“AI doesn’t replace security teams – it gives them superhuman reflexes against evolving threats.”
These advancements demand stronger algorithms capable of withstanding quantum-powered attacks. NIST recently selected four new post-quantum standards designed to protect sensitive data for decades.
Businesses must monitor these developments closely. Implementing hybrid systems that blend classical and quantum-ready protocols ensures smoother transitions as technologies mature. Staying ahead means treating security upgrades as continuous processes – not one-time fixes.
Conclusion
In an era where digital trust is both currency and necessity, protecting sensitive information remains non-negotiable. Our exploration reveals that robust security hinges on understanding core principles – from secret key protocols to advanced algorithms like AES-256. These tools form the backbone of modern privacy, shielding personal and business data from brute-force attacks and unauthorized access.
Organizations must prioritize evolving strategies to match emerging threats. Hybrid systems combining symmetric and asymmetric methods offer flexibility, while innovations like quantum-resistant algorithms prepare us for tomorrow’s challenges. Regular audits, proper key rotation, and AI-driven monitoring create layered defenses against breaches.
The future demands proactive adaptation. As machine learning accelerates threat detection and quantum computing reshapes standards, staying ahead requires continuous learning. We urge teams to implement the best practices discussed – not as optional upgrades, but as foundational requirements.
Mastering digital security isn’t about complexity; it’s about consistent, informed action. Whether safeguarding family photos or corporate assets, the right approach turns vulnerability into confidence. Start today – your data’s integrity depends on it.




